Potential Impacts of Digital Technology on Society
Digital technology impacts a lot on the society especially the human lifestyle. Over the years it has radically increased and has effected the society hardly in the communication to finance and mostly the social interactions.
Its impact:
ADVANTAGES
Adaption-Edges change to adaption and adds improvement to your learning and motivates to engaging content and strategies.
Time-Manages your time as it makes life easier and rapidly if you have the right wireless networks. Influences students and extending learning to having the right educational information.Being the best at learning in time. Pace is not a problem because it allows students to be free and to progress with work at their own rate.
Location-You turn to learn on the go, meaning anywhere anytime. Its creates a new world of opportunities.
Independence-Customises learning level and mortality.
DISADVANTAGES
Affordability-Time changing products as technology takes way and is developed randomly.
Similarities-More of the safe information ,the risk of layering technology and benefiting little.
Old paradigms-Lectures ,administrators being stack in time. The usage of olden technics and digital systems. Lack of lectures introducing new tools of technology.
Balance-Educational balance as more the students parents can't or having difficulty in affording the current digitals network systems e. g latest windows 8.1 and the 3G,4G,wi-fi and tablets etc. All this systems their prices always increase with time.
Technology-It assisting some of the problems and effectively and efficiently dealing and making our learning skills easier and benefiting it has its challenges.
THIS ARE WHAT WE ALL HAVE TO TAKE SERIOUS IN OUR STUDENT DIGITAL SOCIETY.

References:
Canva.com. (2016). Amazingly Simple Graphic Design Software – Canva. [online] Available at: https://www.canva.com/ [Accessed 24 May 2016].
Point, M. (2015). Impact Of Technology On Our Society – Positive & Negative. [online] My Essay Point. Available at: http://myessaypoint.com/how-technology-effects-our-society [Accessed 24 May 2016].

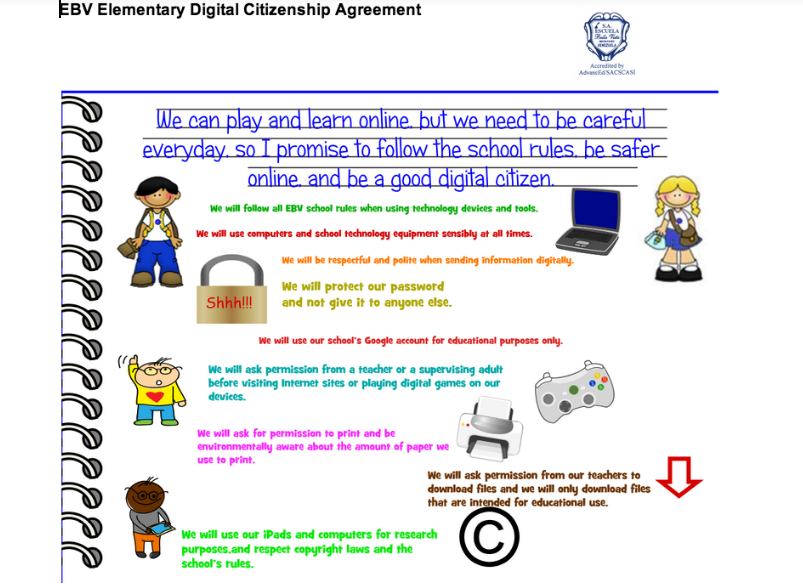

 a society are fully embracing digital commerce. Digital citizenship encourages people to embrace digital commerce and continue to strive for safe and secure utilization of shopping, banking, and engaging in other commercial transactions in technical venues.
a society are fully embracing digital commerce. Digital citizenship encourages people to embrace digital commerce and continue to strive for safe and secure utilization of shopping, banking, and engaging in other commercial transactions in technical venues. As digital citizens, it is our responsibility to develop and continually enhance our technological knowledge. We should support and encourage the acquisition of technological knowledge by others. We should model the positive and proactive use of technology for good causes, personal and professional growth and education.
As digital citizens, it is our responsibility to develop and continually enhance our technological knowledge. We should support and encourage the acquisition of technological knowledge by others. We should model the positive and proactive use of technology for good causes, personal and professional growth and education. f Spider Man's uncle, "With great power comes great responsibility." The global and instantaneous nature of our digital age puts enormous power into the hands of everyday citizens. In order to keep the right to digital access, we must strive to always use it in responsible ways. Sadly, when there is abuse of these rights, the solution is often to withdraw all access (for example, a few students abuse the privilege of having a cell phone at school and thus, all students are banned from using cell phones - even if for an educational endeavor).
f Spider Man's uncle, "With great power comes great responsibility." The global and instantaneous nature of our digital age puts enormous power into the hands of everyday citizens. In order to keep the right to digital access, we must strive to always use it in responsible ways. Sadly, when there is abuse of these rights, the solution is often to withdraw all access (for example, a few students abuse the privilege of having a cell phone at school and thus, all students are banned from using cell phones - even if for an educational endeavor).